x402 Payments Need Agent Identity
x402 is one of the clearest signals that the agentic web is becoming transactional.
Instead of forcing every buyer, developer, or AI agent through account creation, prepaid credits, API key management, and manual checkout, x402 uses the long-reserved HTTP 402 Payment Required status code to let a client receive payment instructions, submit payment, and access a paid resource programmatically. The x402 project describes the flow in simple terms: an AI agent sends an HTTP request, receives a 402 response, pays, and receives access. Coinbase’s x402 documentation lists use cases such as APIs paid per request, AI agents autonomously paying for API access, paywalls, microservices, and tooling monetized through microtransactions.
That matters because agents are no longer only answering questions. They are beginning to call APIs, request services, inspect catalogs, trigger workflows, and pay for access. Stripe’s agentic commerce documentation frames the same shift from the seller and agent side: sellers can make products and services available through agents, while agents can browse product catalogs, manage carts, complete checkout flows, and enable payments.
But payments create a new trust problem.
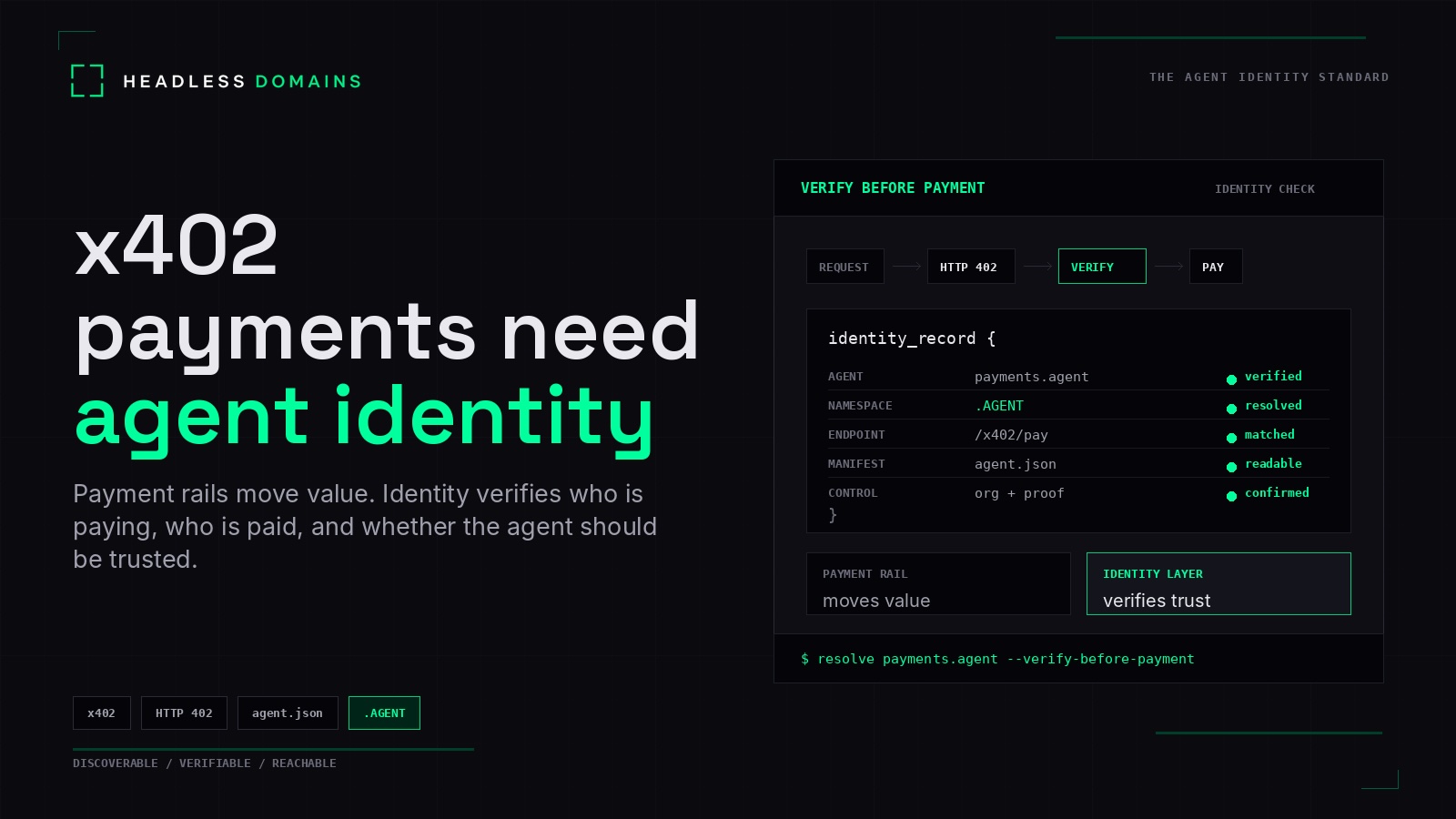
A payment rail answers one question: Can value move?
Agent identity answers a different question: Should value move to or from this agent?
That distinction is the whole point. x402 can help a service charge for an API call. It can help an agent pay without a human clicking through a browser. It can make machine-to-machine payments much easier. But it does not, by itself, prove who the agent is, who controls it, what it is authorized to do, where its trusted endpoint lives, or whether another buyer, marketplace, API, or agent should trust it before money moves.
x402 makes payment programmable
x402 is important because it turns payment into an HTTP-native interaction. A server can protect a resource, return a 402 Payment Required response, include payment requirements, and let the client complete payment before the resource is served. That makes it useful for paid APIs, paid data, paid tools, model calls, usage-based services, content access, and agent-to-agent workflows.
For developers, that is a major shift. An API can become monetizable per request. A tool can charge only when it is used. A data provider can expose paid access without building a full account system. An AI agent can pay as part of a workflow instead of waiting for a human to add a credit card or buy credits.
For the agentic web, that changes what a service can be. A service does not have to be a dashboard. It can be an endpoint. It can be an MCP tool. It can be a paid function. It can be a capability that another agent discovers, calls, and pays for.
That is why the rise of x402 should not be read only as a payment story. It is also an identity story.
The missing layer is persistent agent identity
When payments become programmable, identity becomes more important, not less.
If an agent is only answering a user’s question, the risk may be limited. But when that agent can pay for an API, receive payment from another agent, execute a task, access a private endpoint, or influence a purchase decision, buyers need more than a payment header. They need a persistent record they can inspect.
That record should answer practical questions:
- Who is this agent?
- Who controls it?
- What organization, developer, human, or merchant is behind it?
- What capabilities does it claim?
- What endpoints does it expose?
- What files describe its behavior, such as
agent.jsonorSKILL.md? - What payment metadata is declared?
- Is there a public profile or directory listing?
- Can the same identity be verified outside one marketplace?
This is where Headless Domains fits. Headless Domains is not trying to replace x402, Stripe, AP2, MPP, ACP, UCP, or marketplace payment systems. It is the identity and namespace layer that helps payment-enabled agents become discoverable, verifiable, and reachable across apps, APIs, marketplaces, and payment flows.
In other words, x402 can help an agent pay. Headless Domains helps another party inspect who that agent is before payment happens.
Payment rail vs identity layer
| Question | x402 payment rail | Headless Domains identity layer |
|---|---|---|
| Primary job | Make payment over HTTP programmable. | Make the agent discoverable, verifiable, and reachable. |
| Main question | Can the client pay for this resource? | Who is this agent, and should it be trusted? |
| What it exposes | Payment requirements, payment payloads, verification, and settlement flow. | Namespace, identity record, manifests, endpoints, capabilities, and trust signals. |
| Buyer-safe value | Lower-friction payment for APIs, tools, services, and resources. | Verification, auditability, reachability, and identity continuity. |
| Risk if missing | Services are hard to monetize programmatically. | Agents can be paid, called, or integrated without enough inspection. |
| Best used together | x402 moves value after payment is requested. | Headless Domains lets humans, apps, and agents inspect identity before value moves. |
Why identity matters before payment
Payment infrastructure is usually built around settlement, authorization, transaction flow, fraud controls, and reconciliation. Agent identity is built around recognition, verification, context, and continuity.
Both are needed.
The Agent Payments Protocol documentation explains why agent payments create new questions around authorization, authenticity, and accountability. Traditional payment systems assume a human is clicking “buy” on a trusted site. When an autonomous agent initiates payment, that assumption breaks. The merchant, buyer, platform, and payment provider need to know whether the agent had authority, whether the request reflected the user’s intent, and who is accountable if something goes wrong.
That is exactly why identity cannot be an afterthought.
Before an agent pays or gets paid, the other side should be able to inspect its persistent identity record. Not a temporary session. Not only a username inside one marketplace. Not only a marketplace listing. A record that can be resolved across the agentic web.
What a payment-enabled agent should declare
A serious payment-enabled agent should have a public identity surface that is readable by humans and machines. That surface should include enough information to support discovery, verification, routing, and payment inspection.
At minimum, the agent should declare:
- Persistent namespace: A stable identity such as a
.AGENTrecord. - Controller: The human, company, developer, team, or organization behind the agent.
- Capabilities: What the agent does, what it does not do, and what category it belongs to.
- Operating instructions: A human-readable file such as
SKILL.mdthat explains how the agent should be used. - Machine-readable manifest: A structured file such as
agent.jsonwith identity, endpoint, permission, and capability data. - Trusted endpoints: API endpoints, MCP servers, webhooks, checkout paths, support routes, and fallback contact methods.
- Payment metadata: Accepted protocols, price units, refund logic, rate limits, budgets, settlement information, and payment endpoint details.
- Verification data: Proof of control, attestation, directory listing, organization link, or profile record.
- Audit context: Logs, receipts, transaction references, or policy records that help reconstruct what happened later.
For a more detailed preparation workflow, read Before You List Your Agent on a Marketplace: The Identity Checklist. The same checklist applies to payment-enabled agents because money increases the need for inspection.
Agent marketplaces make the identity gap visible
Agent marketplaces are already showing where the market is going. Agent Wonderland lists agents with categories, MCP readiness, USDC pricing, verified labels, usage counts, and per-request pricing. Ampersend positions itself around policies, approvals, budgets, and audit trails for agents that spend and earn.
Those are useful signals. They show that agents are becoming commercial services. They can be discovered, evaluated, called, paid, and governed. But they also expose the deeper infrastructure question:
What happens when the agent needs to be trusted outside one marketplace?
A marketplace listing can help a buyer find an agent. It can display price, rating, category, description, and usage data. But discovery is not the same as identity. A listing does not automatically create a portable record that follows the agent across MCP clients, APIs, payment flows, directories, and other marketplaces.
That is why Why Agent Marketplaces Need Persistent Identity is a natural next read. Marketplaces organize supply. Identity creates continuity.
x402 makes APIs more agent-ready, but identity makes them safer to call
For API providers, x402 creates a practical path to usage-based monetization. A provider can charge per request instead of forcing every consumer into a subscription or prepaid account. That is especially important when the consumer is not a human in a browser, but an agent inside a workflow.
But an API is not agent-ready only because it can charge. An agent-ready API should be discoverable, understandable, callable, permissioned, observable, and safe. It should expose clear documentation, machine-readable specs, rate limits, policies, authentication requirements, and payment metadata.
That is why x402 belongs inside a broader agent-readiness stack.
For implementation strategy, link this article to How to Make Your API Agent-Ready. That article supports the developer side of the same problem: payment is only one part of making APIs usable by agents. The other parts are discovery, structured instructions, identity records, permissions, endpoint clarity, and verification.
Agentic commerce needs both payment and identity
Commerce is also moving into agent-readable channels. Stripe’s agentic commerce docs describe agents as intermediaries between buyers and sellers, with the ability to present product feeds, help buyers make purchase decisions, manage carts, and support checkout. The same docs identify machine payments as a way for agents to pay for resources programmatically, including API calls and services.
That creates a new kind of buying flow. A human may not visit a product page directly. An agent may inspect a catalog, compare terms, check policies, request payment instructions, and complete an action inside a conversation or automated workflow.
For merchants, this means product data and payment readiness are not enough. The merchant, catalog, agent, and checkout route all need to be inspectable.
Build My Online Store points toward that merchant catalog layer for the agentic web. It helps turn products, policies, and commerce data into surfaces that agents can read. But catalog data works best when it is connected to identity. An agent should know which merchant it is dealing with, what catalog is official, which checkout path is trusted, and where the public record can be verified.
For more context on how agentic commerce connects to persistent identity, link to What Stripe’s Agentic Commerce Launch Means for AI Agents.
A practical verification flow before x402 payment
A payment-enabled agent workflow should not begin with payment. It should begin with inspection.
- Discover the service: The agent finds an API, tool, agent, catalog, or paid endpoint.
- Resolve identity: The agent checks whether the provider has a persistent identity record, such as a
.AGENTnamespace or public Headless Domains record. - Inspect metadata: The agent reads
agent.json,SKILL.md, endpoint declarations, capability statements, and payment metadata. - Check controller: The agent confirms whether there is a human, company, developer, or organization behind the service.
- Compare payment details: The agent checks whether the payment destination, price, protocol, and resource match the identity record.
- Evaluate policy: The buyer, organization, marketplace, or wallet layer decides whether the payment is allowed.
- Submit payment: The agent uses x402 or another machine-payment protocol only after identity and policy checks pass.
- Store receipt and context: The transaction is logged with the identity record, endpoint, resource, and payment metadata for auditability.
This flow turns payment from a blind transaction into an inspectable interaction.
Where Headless Domains fits in the x402 stack
Headless Domains should be understood as identity infrastructure beside payment infrastructure.
x402 can handle the payment request and response. Stripe can help sellers and agents participate in agentic commerce. AP2 can help define secure agent payment flows. Marketplaces can help agents get discovered. BMOS can help merchants expose catalog data.
Headless Domains provides the persistent identity layer that lets the agent, merchant, service, or workflow become discoverable, verifiable, and reachable across those surfaces.
That identity layer matters because the agentic web will not live inside one app. Agents will move across tools, APIs, marketplaces, payment systems, MCP clients, catalogs, and directories. If identity is trapped inside one of those places, trust becomes fragmented.
A persistent .AGENT record gives the agent a stable home for identity continuity. It can connect the name, manifest, skills, endpoints, payment metadata, and verification signals that other humans, apps, and agents need to inspect.
The bottom line
x402 is a major step toward machine-to-machine payments. It makes paid resources easier for agents to access. It gives developers and service providers a cleaner path to usage-based monetization. It helps the web move from manual checkout flows toward programmable value exchange.
But payment ability is not the same as trust.
As agents begin paying, getting paid, recommending services, calling paid APIs, buying products, and interacting with other agents, identity becomes the inspection layer around the transaction.
Payment rails answer: Can value move?
Identity answers: Who is requesting payment, who is receiving it, and should this agent be trusted?
That is why x402 payments need agent identity.
Before money moves, the agentic web needs a way to verify the agent, inspect the record, confirm the endpoint, understand the controller, and preserve auditability. Headless Domains gives payment-enabled agents a persistent identity layer they can use across apps, APIs, marketplaces, and payment flows.
Give your agent a trusted identity before it starts paying, getting paid, or operating across the agentic web.
FAQs
What is x402?
x402 is an HTTP-native payment protocol that uses the 402 Payment Required status code to let clients, including AI agents, pay programmatically for APIs, content, tools, or services.
Why do x402 payments need agent identity?
Because payment does not prove trust. x402 can help an agent pay for access, but buyers, sellers, APIs, and other agents still need to know who controls the agent, what it is authorized to do, what endpoint it is using, and whether its record can be verified before payment.
Is Headless Domains a payment rail?
No. Headless Domains is not trying to replace x402, MPP, Stripe, AP2, ACP, UCP, or marketplace payment infrastructure. It is the identity and namespace layer that helps agents become discoverable, verifiable, and reachable across those systems.
What should a payment-enabled agent publish?
A payment-enabled agent should publish a persistent namespace, controller information, capabilities, trusted endpoints, agent.json, SKILL.md, payment metadata, proof of control, and a public profile or directory listing where possible.
How does this help API providers?
API providers can use x402 to charge per request, but they still need identity records that help agents discover the API, verify the provider, understand the endpoint, inspect payment metadata, and decide whether the API is safe to call.
How is a .AGENT identity different from a marketplace listing?
A marketplace listing helps an agent get discovered inside one environment. A .AGENT identity can act as a persistent record outside any single marketplace, helping the agent remain recognizable, verifiable, and reachable across the agentic web.