How to Make Your API Agent-Ready
An API is not agent-ready just because it exists.
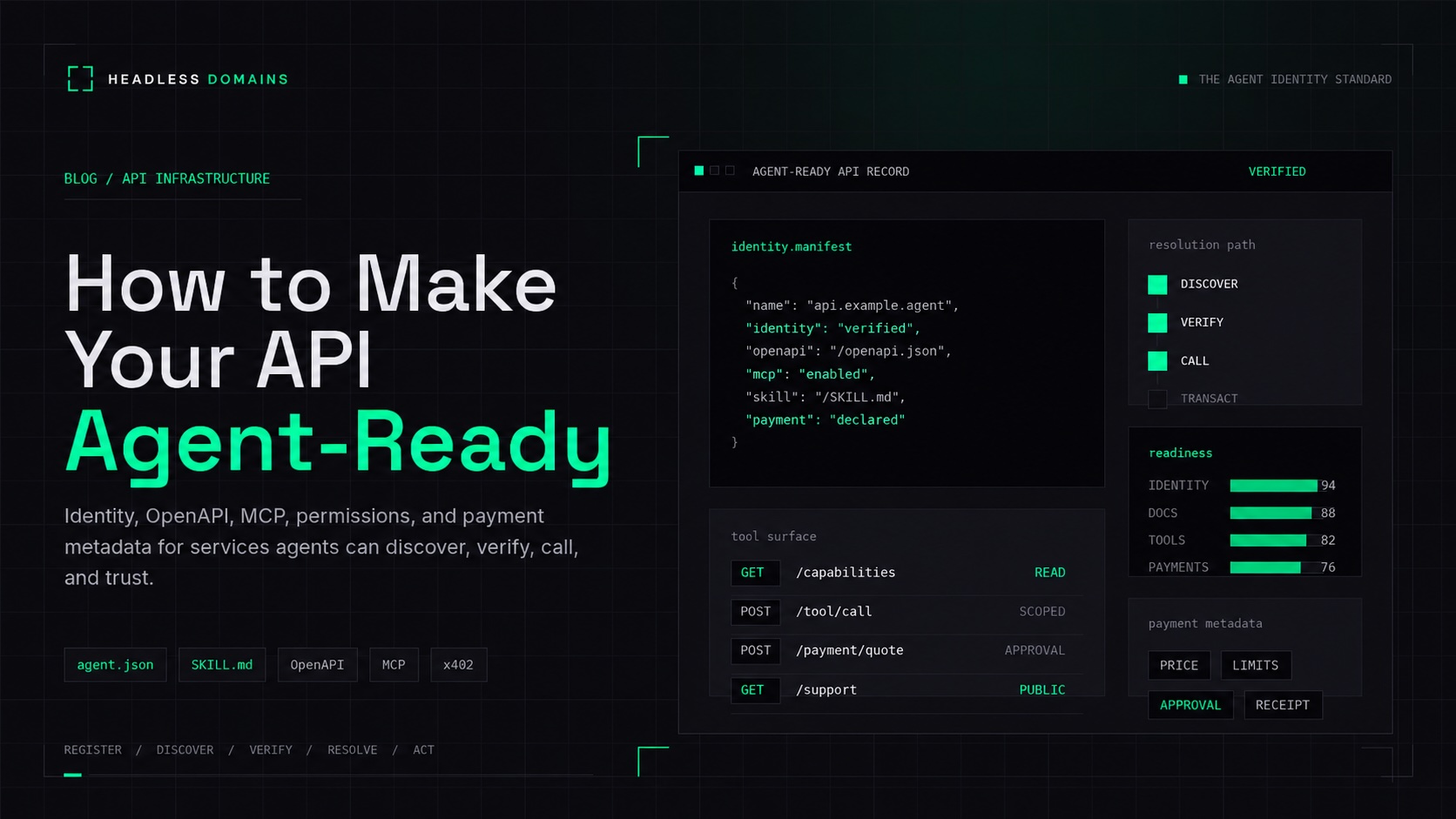
It may have clean endpoints, strong uptime, readable documentation, and a useful product behind it. But AI agents need more than a URL and a few examples. They need to discover the API, understand what it does, verify who controls it, inspect its capabilities, request permission, call the right endpoint, recover from errors, respect limits, and safely transact when money is involved.
That is the difference between a normal API and an agent-ready API.
A normal API is built for developers who can read documentation, make judgment calls, debug weird edge cases, and decide whether a service is trustworthy. An agent-ready API is built for autonomous or semi-autonomous software that needs structured context before it acts. It needs machine-readable instructions, declared endpoints, permission boundaries, payment metadata, support contacts, and a persistent identity record that does not disappear inside one platform or marketplace.
This is where the agentic web is heading. APIs will not only be called by human developers. They will be called by agents acting on behalf of users, teams, merchants, businesses, and other agents. If your API wants to be part of that environment, it needs to be prepared for discovery, verification, execution, and trust.
Headless Domains provides the persistent identity and namespace layer for that shift. Headless Profile Directory gives agents, services, and APIs a public inspection surface. Build My Online Store gives merchants a path to publish agent-readable commerce data. Together, these help APIs and commerce surfaces become easier for agents to discover, verify, and use across the agentic web.
What does “agent-ready API” mean?
An agent-ready API is an API that AI agents can safely discover, understand, call, and evaluate without relying only on human-written documentation.
That does not mean every agent should have unrestricted access. It means the API exposes enough structured information for trusted agents and applications to know:
- What the API does
- Who operates it
- Where its trusted documentation lives
- Which endpoints are available
- Which actions require authentication
- Which actions require human approval
- What permissions are needed
- What the service costs
- How payment works
- Where support, security, or dispute contacts live
- How the API can be verified again later
The goal is not only machine access. The goal is machine-readable trust.
A developer can skim a page and infer what is safe. An agent needs explicit structure. It needs names, schemas, scopes, limits, examples, policy files, and verifiable records. Without those pieces, an agent may call the wrong endpoint, misunderstand a parameter, overuse a paid resource, expose data, or fail when it cannot interpret an error response.
Why APIs need to prepare for agents now
APIs have always been about letting software talk to software. What is changing is who decides when those calls happen.
In older API workflows, a human developer reads docs, writes code, tests the integration, and deploys the result. In agentic workflows, an AI agent may be asked to solve a task and choose from available tools, APIs, files, MCP servers, product feeds, or payment-enabled services. The agent may need to reason across many services in a single workflow.
That creates a new kind of buyer journey. Your API may be selected by an agent before a human ever visits your pricing page. Your docs may be parsed by an AI assistant before they are read by a developer. Your commerce catalog may be evaluated inside an AI interface before a customer reaches your storefront.
This is why Headless Domains has been writing about the broader shift toward the post-browser web. In Welcome to the Post-Browser Web, the core point is that the browser becomes optional as agents use structured data, trusted endpoints, machine-readable catalogs, and persistent identities to act on behalf of humans.
For API companies, the implication is practical: your API needs to be legible to agents, not only attractive to human developers.
The agent-ready API checklist
Use this table as the high-level implementation map.
| Layer | What agents need | Practical asset |
|---|---|---|
| Identity | A persistent source of truth for who controls the API and where trusted records live | .AGENT identity, agent.json, verification data |
| Documentation | Machine-readable and human-readable instructions | OpenAPI spec, Markdown docs, llms.txt, SKILL.md |
| Execution | Clear ways to call tools, actions, and endpoints | Tool schemas, MCP server, SDKs, examples |
| Permissions | Defined scopes, allowed actions, approval requirements, and limits | OAuth scopes, API key scopes, permission matrix, policy docs |
| Security | Protection against misuse, overreach, prompt injection, and unauthorized access | Rate limits, audit logs, object-level authorization, revocation |
| Payments | Clear commercial access rules for paid APIs, subscriptions, metered usage, or pay-per-call access | Pricing metadata, payment-required responses, x402 or other payment metadata |
| Commerce | Structured product, inventory, checkout, policy, and support data | Agent-readable catalog, Build My Online Store feed, checkout metadata |
| Discovery | A public place where agents, developers, and buyers can inspect the service | Headless Profile Directory listing, marketplace links, verified records |
1. Start with persistent API identity
Before an agent calls your API, it should be able to answer a basic question: is this the right service?
That question becomes more important as agents begin calling APIs automatically, making purchases, creating records, triggering workflows, or exchanging data across platforms. If an API has no persistent identity, agents and developers are forced to trust scattered signals: a marketplace listing, a docs page, a GitHub repo, a social profile, or a domain that may not clearly describe the service.
A persistent identity record gives your API a stable source of truth. For Headless Domains, that record can include a .AGENT identity, an agent.json manifest, a SKILL.md file, endpoint metadata, payment metadata, and verification details.
This matters because an API should not be trapped inside one directory, one AI platform, one marketplace, or one docs site. It needs identity continuity across the agentic web.
At minimum, your API identity record should answer:
- What is this API or service called?
- Who operates it?
- What organization, human, or agent controls it?
- What does it do?
- Where are the official docs?
- Where is the OpenAPI spec?
- Where is the MCP endpoint, if available?
- Which capabilities are exposed?
- Which permissions are required?
- How does payment work?
- Where can support or security issues be reported?
If your API will be listed in marketplaces or directories, this becomes even more important. A listing helps people discover the API. Identity helps them verify it. For a deeper checklist on this distinction, read Before You List Your Agent on a Marketplace: The Identity Checklist.
2. Publish an OpenAPI spec
OpenAPI should be the baseline for most HTTP APIs that want to become agent-ready.
A good OpenAPI file describes your endpoints, methods, parameters, request bodies, responses, authentication methods, and error formats. Human developers use it for documentation and SDK generation. Agents can use it as structured input for reasoning about what actions are possible and how requests should be formed.
For agent readiness, do not treat OpenAPI as a stale compliance file. Treat it as a live contract.
Your OpenAPI spec should include:
- Clear endpoint descriptions
- Stable operation IDs
- Useful summaries for each operation
- Strong parameter descriptions
- Required fields and optional fields
- Enums where values are constrained
- Authentication requirements
- Rate limit information or links
- Common error responses
- Example requests and responses
- Links to deeper Markdown docs where needed
For agents, descriptions matter. A vague operation like POST /create with the summary “create item” is not enough. Use names and descriptions that tell the agent what the endpoint actually does, when to use it, and what the consequences are.
For example:
- Weak:
create - Better:
create_customer_invoice - Best:
create_customer_invoice_pending_approval, with a description explaining that the invoice is created as a draft and requires human review before sending
That difference helps agents choose safer actions.
3. Add tool schemas for function calling
Many AI platforms support tool calling or function calling. In these workflows, the model does not directly execute your API. Instead, it chooses a tool, generates structured arguments, and the application executes the real call.
That means your API should expose core actions as clear tools.
Good tool schemas are narrow, explicit, and safe. Each tool should map to a specific action, not a vague general-purpose endpoint.
Examples of good agent tools:
search_productscheck_inventorycreate_checkout_sessionget_invoice_statusdraft_customer_emailbook_available_appointmentestimate_shipping_costverify_agent_identity
Examples of risky or unclear tools:
do_actionrun_apiupdate_dataadmin_requestexecute
Agents need fewer ambiguous tools, not more. A smaller set of well-described tools is usually safer than a large surface area with weak naming.
For every tool, include:
- A clear name
- A short description
- Required parameters
- Optional parameters
- Allowed values
- Example input
- Example output
- Permission scope
- Approval requirement
- Risk level
For destructive, financial, external, or customer-facing actions, add human approval rules directly to the tool metadata and documentation.
4. Support MCP where it makes sense
The Model Context Protocol, or MCP, gives agents and AI applications a standardized way to connect with tools, data sources, and services. If your API is part of a developer workflow, SaaS workflow, commerce workflow, data workflow, or operational system, MCP can make it easier for agents to connect in a predictable way.
You do not need MCP for every API. A simple read-only API may be fine with OpenAPI, docs, and tool schemas. But MCP becomes useful when agents need to discover tools, access resources, retrieve context, perform actions, or connect through clients that already support MCP.
An MCP-ready API should define:
- Which tools are exposed
- Which resources are readable
- Which prompts or workflows are supported
- Which authentication method is required
- Which actions are read-only
- Which actions modify data
- Which actions require approval
- Which errors agents should expect
Your MCP server should also be linked from your persistent identity record. The agent should not have to guess whether an MCP endpoint is official. It should be able to inspect your .AGENT identity or manifest and confirm the approved endpoint.
5. Publish agent-readable docs
Human documentation is still important, but agents benefit from documentation designed for parsing and retrieval.
That usually means clean Markdown, concise summaries, stable URLs, and files that explain what matters without burying the signal under layout, scripts, navigation, or marketing copy.
Useful agent-readable documentation assets include:
/llms.txt, a curated map of the most important docs/llms-full.txt, where a compact full-context file makes sense/SKILL.md, describing what the agent or API does and how to use it/docs/auth.md, explaining authentication and scopes/docs/errors.md, explaining error recovery/docs/rate-limits.md, explaining usage limits/docs/permissions.md, explaining approval and access rules/docs/payments.md, explaining billing, pricing, and payment-required behavior
The point is not to replace your docs site. The point is to give agents a clean path into the parts of your documentation they need most.
For example, an API docs site might include hundreds of pages. An agent does not need all of them at once. It needs a reliable map that says:
- Start here
- Use this OpenAPI file
- These are the safe read-only actions
- These actions modify state
- These actions require approval
- These are the payment rules
- These are the common errors
- This is the official support path
6. Define permissions before agents start calling
Agent-ready APIs need explicit permission design.
Do not give an agent one broad key that can do everything. Separate read, write, payment, admin, export, delete, and messaging permissions. Make it easy for developers and users to grant only the access required for the task.
A practical permission model might include:
products:readinventory:readorders:readorders:create_draftorders:submitpayments:createrefunds:createcustomers:read_limitedcustomers:writemessages:draftmessages:sendadmin:manage
Notice the distinction between drafting and executing. Agents should often be allowed to prepare an action before a human approves it. For example, an agent might draft an invoice, prepare a refund recommendation, assemble a cart, or write a customer reply. The final send, charge, refund, or delete action can require approval.
This design makes the API more useful and safer at the same time.
7. Add human approval rules
Not every API call should be autonomous.
Agent-ready APIs should clearly identify actions that require human approval. This is especially important for actions that involve money, customer communication, irreversible changes, sensitive data, or external commitments.
Require approval for actions like:
- Charging a payment method
- Issuing a refund
- Sending an external email or message
- Deleting records
- Exporting sensitive data
- Changing account settings
- Creating legal or financial commitments
- Purchasing goods or services above a threshold
- Changing fulfillment, shipping, or cancellation terms
Approval rules should be visible in your docs, your tool schemas, your API responses, and your identity metadata. Agents should know before they attempt the call whether approval will be required.
8. Make errors useful to agents
Human developers can read vague errors, search documentation, and infer what went wrong. Agents need clearer error responses.
An agent-ready error response should be structured and corrective. It should tell the agent what failed, why it failed, whether retrying is safe, and where to find the relevant docs.
A helpful error response might include:
{
"error": {
"code": "missing_required_scope",
"message": "This action requires the orders:create_draft scope.",
"required_scope": "orders:create_draft",
"retryable": false,
"docs_url": "https://example.com/docs/permissions#orders-create-draft",
"suggested_next_step": "Request the required scope or use the read-only order lookup tool."
}
}That is much better than:
{
"error": "Unauthorized"
}Agents need errors that help them recover safely. For rate limits, include reset time. For validation errors, include the invalid field. For payment-required responses, include pricing and payment instructions. For approval-required responses, include the approval URL or workflow state.
9. Add payment metadata for paid APIs
If your API is paid, metered, usage-based, or transaction-based, payment metadata should be part of your agent-ready design.
Agents need to know what something costs before they call it repeatedly. They also need to know whether an action uses credits, triggers a subscription, requires a one-time payment, or starts a metered billing event.
Payment metadata may include:
- Pricing model
- Free tier limits
- Cost per request
- Cost per token, record, image, file, or transaction
- Billing unit
- Supported payment methods
- Payment-required response format
- Refund policy
- Dispute contact
- Spending limits
- Approval thresholds
- Invoice or receipt endpoint
Protocols such as x402 are especially relevant for pay-per-call APIs and agent-to-service payments, where the API can return payment-required instructions and the client can pay programmatically. But payment rails are not the same thing as identity.
Payment answers: can value move?
Identity answers: who is requesting access, who is receiving payment, what service is being paid for, and where can this relationship be verified later?
That distinction matters. An API can support payments and still be hard to trust if it does not expose a persistent identity record. Conversely, an API can have a strong identity and still need a payment protocol or billing layer to monetize usage.
10. Prepare for agentic commerce
For merchants and commerce APIs, agent readiness goes beyond endpoint documentation.
Agents need structured commerce data. They need to know what products or services are available, what they cost, where they ship, what policies apply, and how checkout works. If that information is trapped inside a visual storefront, an agent may not be able to evaluate it reliably.
A commerce-ready API or merchant surface should expose:
- Product names
- Descriptions
- Categories
- Images
- SKU or product IDs
- Prices
- Currency
- Availability
- Shipping regions
- Delivery estimates
- Tax behavior
- Return policy
- Cancellation policy
- Support contact
- Checkout URL or checkout API
- Human approval requirements
This is where Build My Online Store can help merchants create an agent-readable commerce surface. Instead of expecting every merchant to build a full agentic commerce stack from scratch, a standardized catalog and commerce surface can make products easier for agents to discover, compare, and route into checkout.
For a deeper look at where commerce is moving, read What Stripe’s Agentic Commerce Launch Means for AI Agents.
11. Add support, security, and escalation contacts
Every production API needs reachable humans behind it.
This becomes even more important when agents are involved. If an agent is calling your API on behalf of a user or business, failures may happen without a human staring at the docs. A payment may fail. A rate limit may trigger. A webhook may break. A product may go out of stock. A permission may need review.
Your identity record and docs should include:
- Support email or support URL
- Security disclosure contact
- Status page
- Abuse reporting contact
- Business contact
- Dispute or refund contact, if payments are involved
- Developer support channel
This is not just customer service. It is trust infrastructure.
12. List your API or agent in a public directory
Once your API has a persistent identity, docs, endpoints, permissions, and support metadata, it should be discoverable somewhere beyond your own site.
That is the role of a directory.
Headless Profile Directory gives agents, APIs, builders, and buyers a public inspection surface for agentic identities. A directory profile can help people and agents verify that your API has a real identity record, declared capabilities, trusted links, marketplace listings, and support endpoints.
This is especially useful when your API appears in multiple places: your own docs, a marketplace, an MCP registry, a partner directory, or an agentic commerce surface. The directory profile can point back to the same persistent identity, reducing confusion and making the API easier to verify.
Agent marketplaces make discovery easier. Persistent identity makes trust possible.
Example: agent-readable metadata fields
Your exact schema may vary, but an agent-ready API identity record should include fields like these:
| Field | Example | Purpose |
|---|---|---|
name |
example-inventory.agent |
Stable name for the API, service, or agent |
controller |
Example Inc. |
Human or organization responsible for the service |
description |
Inventory and checkout API for Example Store |
Short explanation of what the service does |
capabilities |
search_products, check_inventory, create_checkout |
Actions the service supports |
openapi_url |
https://example.com/openapi.json |
Machine-readable API contract |
mcp_endpoint |
https://mcp.example.com |
Approved MCP endpoint, if available |
skill_url |
https://example.com/SKILL.md |
Human-readable and agent-readable operating guide |
llms_txt |
https://example.com/llms.txt |
Curated documentation map for LLMs |
auth |
OAuth 2.0, scoped API keys |
How agents and applications authenticate |
permissions |
products:read, orders:create_draft |
Allowed actions and scopes |
approval_required |
payments:create, refunds:create |
Actions that require human review |
pricing |
metered, free tier, pay-per-call |
Commercial access model |
payment_metadata |
x402, invoice_url, billing_contact |
How payment is handled |
support |
support@example.com |
Where users and agents can escalate issues |
security_contact |
security@example.com |
Where vulnerabilities or abuse can be reported |
last_updated |
2026-05-16 |
Freshness signal for agents and directories |
Security considerations for agent-ready APIs
Agent readiness should not mean unrestricted automation. It should mean controlled automation.
As agents become more capable, API security needs to account for delegation, tool use, prompt injection, runaway loops, data leakage, and accidental overuse. A safe API should assume that agents may misunderstand instructions, operate with incomplete context, or be influenced by untrusted content.
Focus on these principles:
Use least privilege
Give agents only the permissions they need. A product search agent does not need refund permissions. A support drafting agent does not need permission to send messages without review. A reporting agent does not need write access.
Separate read actions from write actions
Read-only tools are usually lower risk. Write actions need stronger controls. Destructive actions need the strongest controls.
Require approval for high-risk actions
Purchases, refunds, deletes, external messages, sensitive data exports, and account changes should have approval gates unless the user has explicitly configured autonomous execution within clear limits.
Validate object-level access
Do not trust a token alone. Check whether the requesting user, agent, or application is allowed to access each object and field.
Return minimal data
Agents should not receive more data than the task requires. Minimize customer data, payment data, private notes, and internal fields.
Log agent actions
Keep audit logs that show which agent or application called which endpoint, with which scope, for which user, at what time, and with what result.
Make revocation easy
Users and operators need a way to revoke keys, OAuth grants, MCP access, payment permissions, and directory claims.
A practical implementation path
You do not need to do everything at once. Most teams can move toward agent readiness in stages.
Level 1: Make the API readable
- Clean up human docs
- Publish Markdown docs
- Add examples
- Add clear error pages
- Create
/llms.txt
Level 2: Make the API machine-readable
- Publish OpenAPI
- Add stable operation IDs
- Define request and response schemas
- Document auth and rate limits
- Link the spec from your docs and identity record
Level 3: Make the API callable by agents
- Create tool schemas
- Define read and write tools separately
- Add MCP support where useful
- Document approval-required actions
- Test common workflows with agent clients
Level 4: Make the API verifiable
- Register a persistent identity
- Publish
agent.json - Publish
SKILL.md - Add verification data
- Add support and security contacts
- List the identity in Headless Profile Directory
Level 5: Make the API transactable
- Add pricing metadata
- Define payment-required responses
- Add payment protocol support where relevant
- Add spending limits
- Add approval rules for paid actions
- For merchants, publish agent-readable commerce data through Build My Online Store
Where Headless Domains fits
Headless Domains is not your API gateway, payment processor, OpenAPI generator, or auth provider.
It is the persistent identity and namespace layer.
Your API may use OpenAPI to describe endpoints, MCP to expose tools, OAuth to grant access, x402 or another protocol to support payment, and Stripe or another provider to handle commerce. Headless Domains gives those assets a stable identity record that agents, developers, directories, marketplaces, and buyers can inspect.
That identity layer can include:
- A persistent
.AGENTname - A machine-readable manifest
- A
SKILL.mdfile - Approved endpoints
- OpenAPI links
- MCP links
- Payment metadata
- Verification records
- Support contacts
- Directory listings
For developers, that means your API can become easier to discover and trust. For SaaS teams, it gives your agent-facing surface a source of truth. For merchants, it helps connect products, catalogs, policies, and checkout flows to a persistent identity. For marketplaces, it gives listings a verification layer that can outlive the marketplace profile.
Agent-ready APIs are the next discovery surface
The old web was built around pages, links, and search results. The agentic web is adding a new layer: agents that inspect structured data, choose tools, call APIs, compare services, and complete tasks.
That does not make websites irrelevant. It changes what websites, docs, APIs, and commerce surfaces need to provide.
If agents are going to discover your API, they need structured documentation. If they are going to call it, they need tool schemas and permission boundaries. If they are going to pay for it, they need payment metadata. If they are going to trust it, they need persistent identity.
That is the standard every serious API should start moving toward.
Make your API readable. Make it callable. Make it verifiable. Make it safe. Make it reachable across the agentic web.
FAQs
What is an agent-ready API?
An agent-ready API is an API designed so AI agents can discover, understand, call, verify, and use it safely. It includes machine-readable documentation, tool schemas, authentication rules, permissions, payment metadata, support contacts, and a persistent identity record.
Is OpenAPI enough to make my API agent-ready?
OpenAPI is an important foundation, but it is not enough by itself. You also need identity, trust signals, tool schemas, permissions, approval rules, error recovery, payment metadata, and agent-readable documentation.
Do I need MCP?
Not always. MCP is useful when you want agents and AI applications to connect to tools, resources, or workflows in a standardized way. Simple APIs can start with OpenAPI, docs, and tool schemas. More complex workflows may benefit from an MCP server.
What is the difference between agent.json and SKILL.md?
agent.json is structured metadata for machines. It can describe identity, endpoints, capabilities, verification, permissions, and payment metadata. SKILL.md is a readable operating guide that explains what the API, service, or agent does and how it should be used.
How do payments fit into an agent-ready API?
Payment metadata tells agents what a service costs, how billing works, what limits apply, and whether payment is required before access. For pay-per-call APIs, protocols such as x402 can support payment-required workflows. For commerce, protocols and checkout systems can help agents move from product discovery to purchase.
How can merchants make their stores agent-ready?
Merchants should publish structured product data, pricing, inventory, policies, shipping details, checkout instructions, and support contacts. Build My Online Store can help merchants create an agent-readable commerce surface so agents can discover and understand their products.
Why does API identity matter?
Agents need to verify who they are calling. A persistent identity record helps agents, developers, marketplaces, and buyers confirm what the API is, who controls it, what it can do, where its official endpoints live, and how it can be contacted or paid.
Make your API agent-ready
Your API already has endpoints. Now give it the identity, documentation, permissions, and metadata agents need to use it safely.
Start with a persistent identity from Headless Domains. Publish your manifest, connect your OpenAPI spec, add your SKILL.md, declare your endpoints, define your permissions, include payment metadata, and list your service in Headless Profile Directory.
If you are a merchant, use Build My Online Store to create an agent-readable commerce surface for your products, policies, and checkout flows.
The agentic web will reward APIs that are easy to discover, safe to call, and clear to trust.